Publicly released court records, Department of Justice productions and investigative reporting map Jeffrey Epstein’s conventional online footprint — emails, attachments, calendars, flight logs, photos and deposition exhibits — but despite widespread forum speculation, there is no publicly disclosed forensic proof that Epstein personally used Tor or operated on the dark web.
What the public record shows
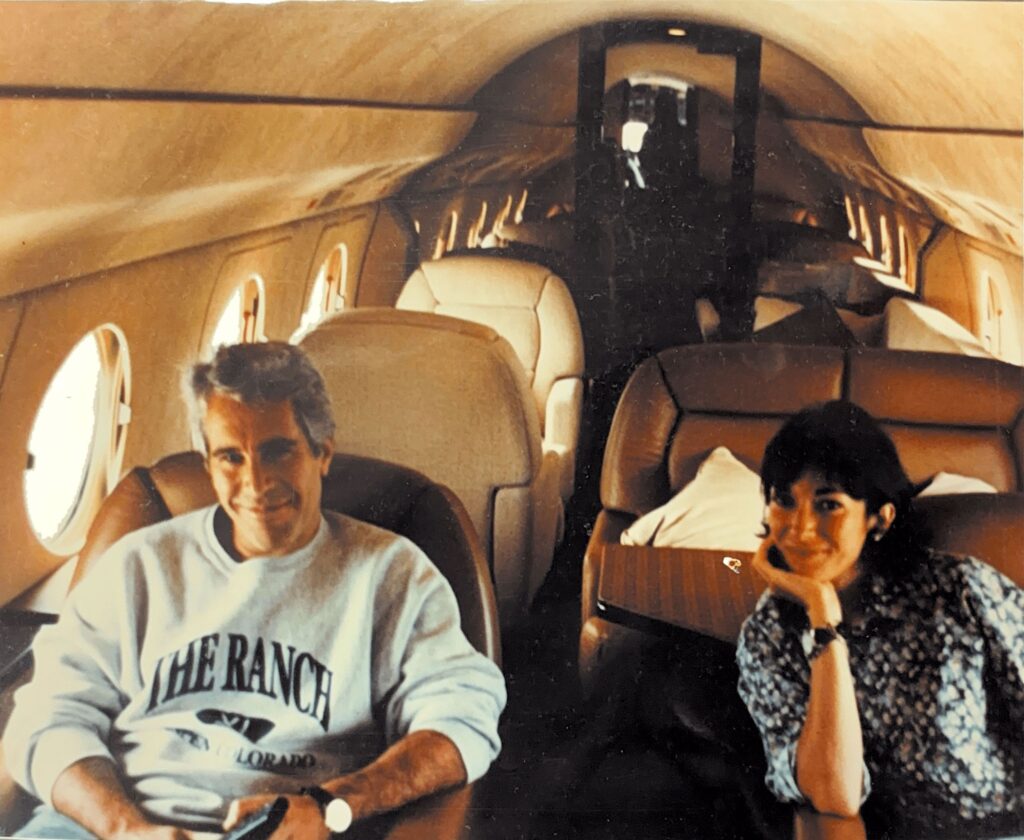
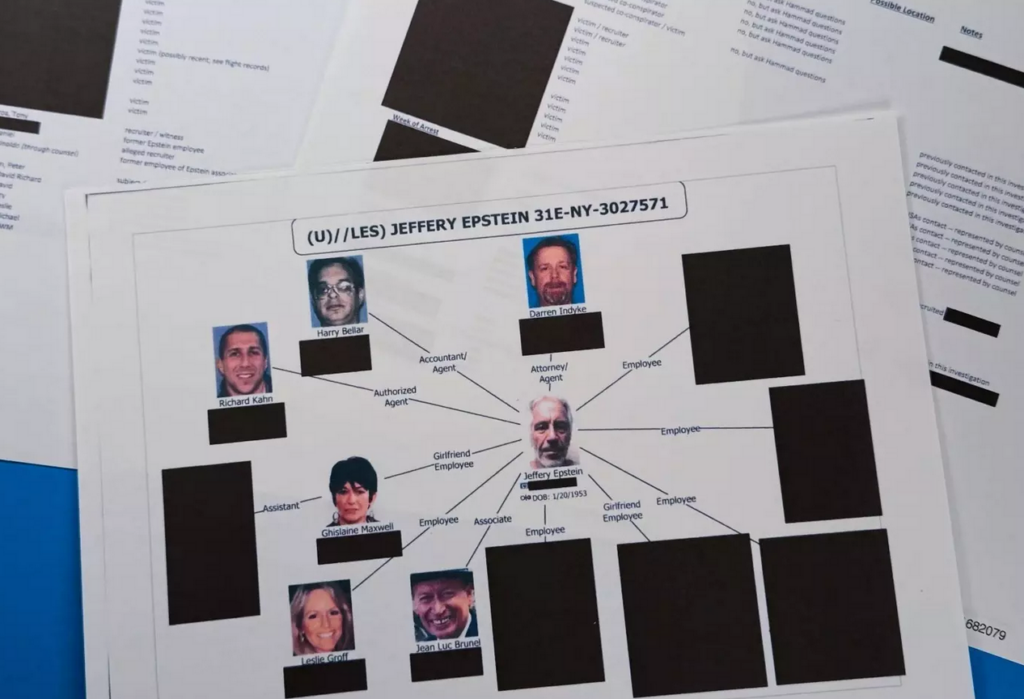
The most substantial materials about Epstein’s communications and activities are standard internet artifacts produced in civil litigation and government investigations: email batches and attachments, scanned exhibits, calendar entries, flight manifests and surveillance video. Large, consolidated releases — notably the DOJ’s multi‑dataset disclosures and congressional releases — have placed millions of pages, images and videos into the public domain. These materials document who Epstein communicated with, travel patterns, photographed evidence and witness statements; they are conventional files (email headers, PDFs, scanned photos) rather than technical traces associated with Tor hidden services or darknet marketplaces.
Major public productions and media coverage
- Department of Justice disclosures: The DOJ consolidated and published massive datasets of responsive files under the Epstein Files Transparency Act and related releases (DOJ public portal and press statements describing multi‑million‑page productions). These datasets include court records, FBI and DOJ documents, CBP flight logs, videos and other exhibits, and DOJ officials have cautioned the public that the volume includes duplicates and material submitted by members of the public.
- Congressional and media packages: House Oversight releases and major newsrooms (BBC, CBS News and others) have reviewed and republished key exhibits and findings from the unsealed materials, highlighting items such as flight logs, internal emails and jail surveillance video. Journalists have used those primary documents to reconstruct timelines and flag specific communications, but their reporting documents conventional evidence rather than technical dark web forensics.
What the record does not show — crucial gaps
Despite the torrent of documents and the proliferation of online rumors, the public record lacks authenticated forensic artifacts tying Epstein directly to the dark web:
No published Tor server or client logs, authenticated hidden‑service records, or ISP/Tor exit‑node correlations have been disclosed in DOJ or court productions that prove Epstein personally used Tor.
No publicly authenticated cryptocurrency forensics (wallet ownership tied to Epstein via on‑chain evidence plus off‑chain attribution) have appeared in releases as proof of his operational use of darknet marketplaces.
Many “leaks” and forum claims are user‑generated and unverified; the DOJ itself acknowledged its mass production may include false or fabricated submissions that were part of the files it received.
Why dark web claims spread
Two factors amplify confusion. First, the sheer scale of disclosures — millions of pages, thousands of images and hundreds of videos across multiple releases — invites amateur analysis, misattribution and out‑of‑context interpretation. Second, associative reasoning on forums (seeing names, IP fragments, vendor records or opaque technical terms) encourages conflation: mentions of third parties’ online activity or business vendors can be misconstrued as Epstein’s own technical behavior. Darknet and conspiracy communities further amplify sensational claims, which then migrate to mainstream comment threads and blogs.
Associates versus direct evidence
Court exhibits and depositions frequently reference associates, staff, vendors and third parties who appear in emails or financial records. Those connections merit scrutiny, but they are not, by themselves, proof that Epstein personally operated on Tor or ran darknet services. Responsible reporting should avoid equating mention or proximity with technical involvement absent corroborating forensic logs or prosecutorial disclosures.
Conclusion
The public corpus now available gives a far fuller picture of Epstein’s conventional online and paper trail — emails, flight logs, photos and sworn testimony — and it has enabled journalists and researchers to assemble detailed timelines and contact maps. But despite intense public interest and widespread forum speculation, the materials released to date do not include authenticated technical forensics that show Epstein personally used Tor or ran darknet marketplaces. Claims linking him directly to operational dark‑web activity remain unproven in the publicly disclosed record; further forensic disclosure or prosecutorial evidence would be required to change that assessment.

